thecomputerguy
Well-Known Member
- Reaction score
- 1,487
Non-MSP client compromised, usual thing, token theft.
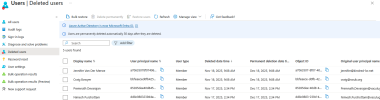
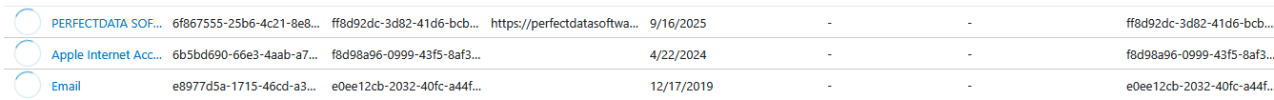
The weird thing about this one is that they purchased 3 domains through their tenant through M365, using my clients saved payment info then created users, then deleted the users. So the users are now sitting in the deleted users section. (vacalug.net and swuk.org are the other two).

They changed some contact info in azure.
I don't see the point of this here.
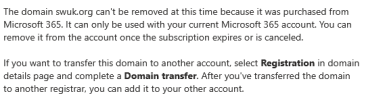
When I try to delete the domain out of the tenant I get:
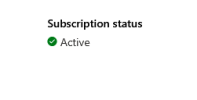
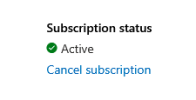
When I go into the billing section for the purchase there is no option to cancel the subscription ... only to disable recurring billing:
What in the world ... they obviously got a hold of the credential's for one of the GA's. This is not a best practice place, they are a landscaping company with 5 people so best practice and ongoing support isn't a thing for them.
The weird thing about this one is that they purchased 3 domains through their tenant through M365, using my clients saved payment info then created users, then deleted the users. So the users are now sitting in the deleted users section. (vacalug.net and swuk.org are the other two).

They changed some contact info in azure.
I don't see the point of this here.
When I try to delete the domain out of the tenant I get:
When I go into the billing section for the purchase there is no option to cancel the subscription ... only to disable recurring billing:
What in the world ... they obviously got a hold of the credential's for one of the GA's. This is not a best practice place, they are a landscaping company with 5 people so best practice and ongoing support isn't a thing for them.