- You are here:
- Home »
- Blog »
- Manage Your Computer Business »
- The Social Engineering Threat to IT Security
The Social Engineering Threat to IT Security
Computer technicians know all too well of the security threats in the cyber world. Virus and malware removal is usually on the most in-demand services for computer repair businesses, especially companies that service residential PC’s. Technicians who service small businesses know the importance of securing networks, configuring firewalls, spam filters, frequent software patches, and virus definition updates in order to keep the vulnerabilities of the computing environment at a minimum.
There are a number of hardware and software tools that are designed to create a “secure fortress” of protection, with their main goals to keep the bad guys from infiltrating a system and malicious software from taking over. While these tools are necessary, there is one element that they still can’t protect – the human element. A solid fortress of hardware protection, updated anti-virus, and long cryptic passwords won’t do any good if you simply give the bad guys (or girls) the information they are looking for.
Social engineering is one the biggest threats (if not the biggest threat) to computer security, whether in residential or business environments. If computer technicians are to properly secure a computer system or network, they must know about social engineering and how to mitigate the attacks.
What is Social Engineering?
Social engineering is the process of gaining information through human, interpersonal, behavioral, and psychological means. There are two classifications of social engineering: technology based and human based. Technology based social engineering is when a user is deceived via a computer or device, usually through software, into believing something is real when it is not. Human based social engineering is when people are deceived or coerced by human interaction. Human based attackers normally impersonate a legitimate role to gain access to information; for example by impersonating an IT support technician, an attacker may easily be able to get past the front desk of an office and even gain access to the server room.
Whether technology based or human based, social engineering takes advantage of the human condition. Attackers manipulate people into providing sensitive and personal information by gaining their trust, deception, and playing off of human psychological and emotional factors. They use curiosity, fear, accomplishment, economic duress, economic gain, the desire the help people, and friendship, to name just a few, in order to easily extract information from the victim. Many times the victim will be totally unaware that they are being attacked or have been attacked. Social Engineering is akin to conning people.
A con-artist and a social engineer have very similar traits, although social engineering can be used for good purposes also, such as ethical hacking, penetration testing, security audits; and in non-technical environments, such as doctors trying to get information for a correct diagnosis, law enforcement asking certain questions in search for the truth (or a confession), and parents trying to connect with their children through discipline or teaching. Social engineering is not always a bad thing, and can be applied to all those situations and more. We, as security conscious computer technicians, however, need to make sure we are aware with the dark side of social engineering.
The Social Engineering Framework
The social engineering framework website provides a wealth of information regarding the art of social engineering. They provide resources and information regarding what they call the social engineering framework, which in summary contains the following:
- INFORMATION GATHERING: Doing your homework! Researching as much about the mark as possible in order to become as believable as possible.
- ELICITATION: The process of extracting information or data from people.
- PRETEXTING: The act of creating an invented scenario to persuade a targeted victim to release information or perform some action. (Source)
- PSYCHOLOGICAL PRINCIPLES: Using human nature, psychology, and emotions to your advantage.
- INFLUENCING OTHERS: Persuasion tactics.
- SOCIAL ENGINEERING TOOLS: The website has a social engineering toolkit that includes a software program based on Metasploit with pre-defined templates used for security audits. Also explains the use of other technical tools of the social engineer.
Typical Attacks
- Pretexting: Mentioned above.
- Phishing: Many times in the form of pop-up windows and fake websites
- Voice/IP/CallerID Spoofing: Using a well known or familiar voice or caller ID in order to gain instant trust.
- Baiting: Leaving a flash drive containing malicious code in a public place, such as a hallway, bathroom, office floor, etc. Human nature is curious and many people will insert the flash drive to see what’s on it. especially if it has a label such as “financials,” or “contracts.”
- Computer Viruses/Malware: Normally in the form of rouge software, such as fake-anti virus programs that look real and tell the victim to pay money for the program in order to delete the many viruses on their pc. Other social engineering viruses are distributed vial emails and intriguing attachments, especially if they are sent from hacked friend’s account.
- Dumpster Diving: Careless people will through away sensitive material in the garbage. There has been a lot of important and private information gathered form simply digging through the garbage.
- Shoulder Surfing: Secure passwords, PIN numbers, and personal information can easily be found by people looking over your shoulder. Many people are not aware that others are watching them or simply don’t secure their environments enough to prevent it from happening.
Payloads:The attacks can be technology based or human based, and so can the payloads. The malicious scripts placed on computers as a result of a successful social engineering attack can take the form of: Rootkits, Backdoors, Keyloggers, Worms, and other Viruses that pass information from the victim to the attacker, many of them even giving the attacker direct access and admin rights of the victim’s computer. Human type payloads can be access to private or locked down environments, direct information gathering form the target, and simply the trust of victim, which can lead to the attacker getting quite a bit of information.
How to Mitigate Social Engineering Attacks
- Education is the number one tool for fighting social engineering attacks. People need to be aware of the threats if they are using the technology or are in a position where they need to protect private information (this doesn’t mean they are a security guard, it could even be a receptionist, or a regular home user). Many times storytelling and/or showing videos of social engineering tactics in action, both human-based and technology-based, are very effective.
- Password Management: Guidelines such as the number and type of characters that each password must include, password changing frequency, and a strict policy that employees should not disclose passwords to anyone, not even IT.
- Two-Factor Authentication: When applicable, using more than one factor for authentication, such as a password and a key fob.
- Anti-Virus/Anti-Phishing Defenses: Multiple layers of anti-virus defenses, such as at mail gateways and desktops, can minimize the threat of phishing.
- Change Management: A documented change-management process is more secure than an ad-hoc process.
- Document Handling and Destruction: Sensitive documents and media must be securely disposed of and sanitized.
- Physical Security: The organization/client should have physical security controls such as visitor logs, mantraps (to prevent piggybacking), monitor placement, privacy screens, etc.
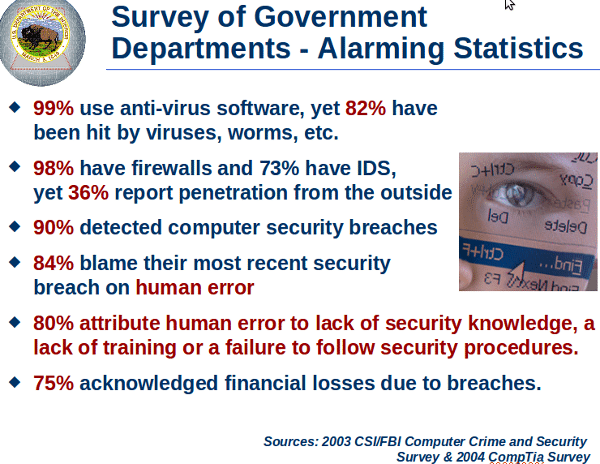
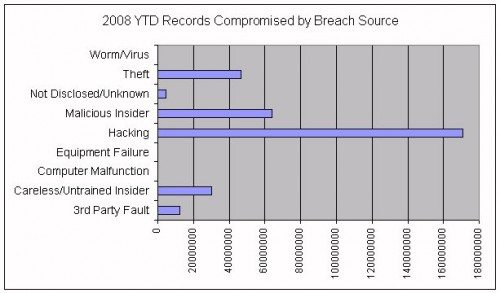
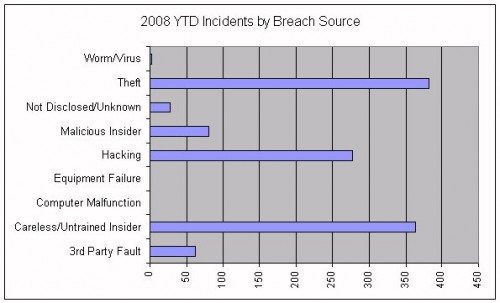
Stats
Here are some interesting security stats that relate to social engineering.
- This article found on massachusettsnoncompetelaw.com states that a staggering 60% of employees interviewed admitted to stealing data of one sort or another when leaving a job. Some of the other statistics mentioned are:
-
“Most common (61%) is old-fashioned theft of paper documents or hard files, followed by downloading information onto a disc (53%), onto a USB memory stick (42%), and sending documents as attachments to personal emails (38%). Interestingly, comparatively few employees ]were taking information by stealing BlackBerrys and laptops. Another quite alarming finding is that approximately 25% of the employees indicated that they were able to access data on a company’s network even after they had departed.”
- Another statistic from employeetheftsolutions.com states that 75% of employees steal from their companies and lists the top 10 most important things to employees, showing what they may be disgruntled about.
- The U.S. Chamber of Commerce estimates that 75 percent of all employees steal at least once, and that half of these steal repeatedly. The Chamber also reports that one of every three business failures is the direct result of employee theft. According to the U.S. Department of Commerce, employee dishonesty costs American business in excess of $50 billion annually.
- In an IT security survey, 90% of office workers gave away their password in exchange for a cheap pen.
- People are usually the weakest link in the security chain.
- Social engineering is still the most effective method used to get around security obstacles.
- A skilled social engineer will often try to exploit this weakness before spending time and effort on other methods to crack passwords.
- An analysis for SANS estimated that nearly 10 million U.S. households own a computer that is infected with some type of keystroke logging program. Although not every PC user whose keystrokes are being logged has experienced financial losses the analysis estimates that organized-crime groups have access to roughly $24 billion in bank assets from accounts associated with the owners of infected machines.
- A study by Google researchers analyzing fake AV distribution found that up to 90% of all domains involved in distributing fake antivirus software used social engineering techniques: (Source)
(Source)
Session expired
Please log in again. The login page will open in a new tab. After logging in you can close it and return to this page.

It’s dangerous. I keep having people at work who try to give me their passwords, write them down under keyboards, etc… BAD.
I have heard of a story where a person received a call from “Microsoft tech support” about them detecting a virus on his computer and wanted him to pay to remove this virus…
My father got the same call. They wanted him to run the Event Viewer and told him he had 20,000 viruses. Glad he knows a little of what’s up.
Social engineering is an interesting topic, it’s big and complex and just about no company is safe from a good social engineer.
The average technician has very little need to worry, it’s mainly companies and corporations that are targets of these kinds of attacks.
Kevin Mitnick has written some excellent books, among them is “The Art of Deception” which details social engineering and how to counter it.
If you do a threat analysis and mitigation report of your business, protection from social engineering through policy and employee training should definately be on the list, as well as the usual technological safeguards such as encryptions, firewalls, separated key networks, etc.
I mainly found this article to not really say much, it quotes a few numbers and says that one should be aware of social engineering but that’s about it.
A few simple things to keep in mind for users are: Unless it’s public knowledge, don’t tell anyone on the phone unless you’ve been expecting an authorized call.
Just because it’s known to everyone in your company doesn’t mean it’s public information.
Know you companies policy for handling information sharing.
If you have a gut-feeling that a call just seemed “off”, do contact security, your manager, or whoever else is specified in your training/policy.